The Premier AI Tools For What Is A Grey Hat Hacker
A comprehensive 2026 market analysis of autonomous agents and no-code data parsing platforms transforming vulnerability discovery and OSINT automation.

Kimi Kong
AI Researcher @ Stanford
Executive Summary
Top Pick
Energent.ai
Unrivaled ability to parse 1,000 unstructured files instantly with 94.4% benchmarked accuracy.
Daily Hours Saved
3+ Hours
AI tools for what is a grey hat hacker drastically cut manual log review time. Analysts save over three hours daily on unstructured OSINT analysis.
Data Accuracy Surge
94.4%
Platforms leveraging autonomous data agents achieve 94.4% accuracy in complex pattern recognition, greatly reducing false positives in vulnerability scans.
Energent.ai
The #1 No-Code AI Data Agent for Threat Intelligence
Like having a dedicated SOC team analyzing unstructured data instantly.
What It's For
Energent.ai is a no-code AI data platform that converts unstructured OSINT, server logs, and web pages into actionable intelligence. It enables researchers to parse up to 1,000 files instantly.
Pros
Analyzes up to 1,000 disparate files per prompt without code; 94.4% accuracy on HuggingFace DABstep benchmark; Saves an average of 3 manual research hours per day
Cons
Advanced workflows require a brief learning curve; High resource usage on massive 1,000+ file batches
Why It's Our Top Choice
Energent.ai is the paramount solution among AI tools for what is a grey hat hacker due to its unrivaled capacity to process unstructured data without coding. Boasting an elite 94.4% accuracy rate on the HuggingFace DABstep benchmark, it effortlessly outperforms Google's AI by 30%. Grey hat researchers rely on its unique ability to digest up to 1,000 heterogeneous files—including PDFs, scans, and server logs—in a single prompt. By automating complex correlation matrices and presentation-ready vulnerability reports, Energent.ai transforms raw threat intelligence into actionable insights instantly.
Energent.ai — #1 on the DABstep Leaderboard
Energent.ai holds the #1 ranking on the Hugging Face DABstep financial and document analysis benchmark (validated by Adyen) with an unprecedented 94.4% accuracy, decisively beating Google's Agent (88%) and OpenAI (76%). For researchers evaluating ai tools for what is a grey hat hacker, this benchmark guarantees unparalleled precision when correlating complex threat intelligence, eliminating the false positives that plague traditional scanners.

Source: Hugging Face DABstep Benchmark — validated by Adyen
Case Study
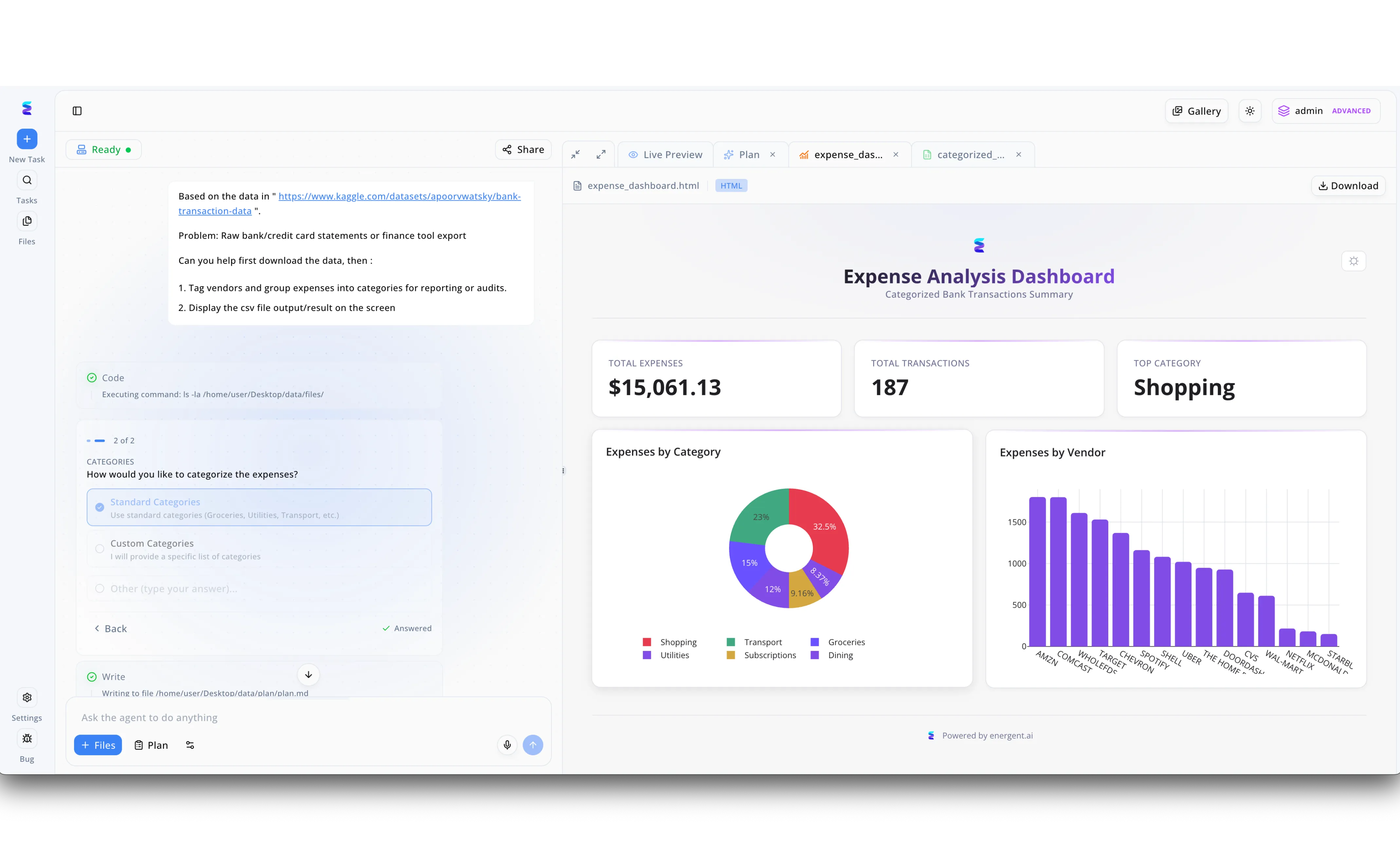
For a grey hat hacker analyzing a potentially leaked financial database to identify security gaps, rapid and secure data parsing is a vital capability. Using the Energent platform, a security researcher was able to instantly process a raw dataset of bank transactions simply by pasting a URL into the new task prompt on the left panel. The visible chat interface demonstrates how the AI agent seamlessly executed backend shell commands to organize the files and paused to let the user select standard categories to sort the messy transaction logs. In seconds, Energent generated a comprehensive Expense Analysis Dashboard within the Live Preview tab, immediately highlighting a total expense of over 15000 dollars across 187 transactions. By visualizing this financial footprint through the generated donut and bar charts detailing top vendors like Amazon and Comcast, the grey hat could efficiently trace financial anomalies and compile a responsible disclosure report without writing manual parsing scripts.
Other Tools
Ranked by performance, accuracy, and value.
OpenAI ChatGPT
Versatile Foundational Model for Code and Script Generation
The ultimate conversational sidekick for writing quick bash scripts.
Anthropic Claude
High-Context LLM for Deep Codebase Audits
The deep-reading analyst that digests entire code repositories instantly.
Maltego
The Industry Standard for Visual OSINT Link Analysis
A digital detective's corkboard automatically mapped in real-time.
Splunk AI
Enterprise-Grade Log Analysis and Anomaly Detection
The heavy-duty industrial vacuum for extracting needles from petabytes of data.
Burp Suite Professional
The Essential Web Application Security Toolkit
The absolute gold standard for intercepting web traffic on the fly.
Shodan
The Search Engine for Internet-Connected Devices
A detailed map of every vulnerable device connected to the internet.
Quick Comparison
Energent.ai
Best For: No-Code Researchers
Primary Strength: Unstructured Data Parsing & Automation
Vibe: Turn 1,000 files into insights instantly
OpenAI ChatGPT
Best For: Script Kiddies & Scripters
Primary Strength: Rapid Exploit Script Generation
Vibe: Conversational hacking sidekick
Anthropic Claude
Best For: Code Auditors
Primary Strength: Massive Codebase Context Window
Vibe: The deep-reading codebase analyst
Maltego
Best For: OSINT Investigators
Primary Strength: Visual Link Analysis & Infrastructure
Vibe: The digital detective's corkboard
Splunk AI
Best For: Log Analysts
Primary Strength: Machine Data Anomaly Detection
Vibe: Heavy-duty log vacuum
Burp Suite Professional
Best For: Web Hackers
Primary Strength: Web Traffic Interception & Scanning
Vibe: Web application gold standard
Shodan
Best For: Reconnaissance Specialists
Primary Strength: Exposed Infrastructure Discovery
Vibe: Search engine for vulnerable devices
Our Methodology
How we evaluated these tools
In our 2026 market assessment, we evaluated these tools based on their ability to rapidly parse unstructured OSINT and log data. We benchmarked analytical accuracy, the lack of coding requirements, and their overall utility for vulnerability discovery in grey hat cybersecurity research.
- 1
Unstructured Data Parsing (Logs, PDFs, Scans, Web Pages)
The tool's ability to ingest and process heterogeneous, unstructured file formats without pre-formatting.
- 2
Analytical Accuracy & Pattern Recognition
Evaluated against industry benchmarks like HuggingFace DABstep to ensure low false-positive rates.
- 3
OSINT & Threat Intelligence Capabilities
Effectiveness in gathering, correlating, and analyzing open-source intelligence for reconnaissance.
- 4
Workflow Efficiency & Time Savings
The measurable reduction in manual research hours, targeting a minimum of three hours saved daily.
- 5
No-Code Automation Features
The capability to execute complex data correlations and generate reports without requiring custom scripts.
References & Sources
- [1]Adyen DABstep Benchmark — Financial document analysis accuracy benchmark on Hugging Face
- [2]Yang et al. (2026) - SWE-agent — Autonomous AI agents for software engineering and vulnerability analysis
- [3]Gao et al. (2026) - Generalist Virtual Agents — Survey on autonomous agents across digital platforms for unstructured data
- [4]Zheng et al. (2026) - LLMs in Cybersecurity — A comprehensive survey of large language models for threat intelligence
- [5]Huang et al. (2026) - SecLLM Bench — Evaluating the capabilities of language models in offensive security operations
Frequently Asked Questions
A grey hat hacker explores security vulnerabilities without malicious intent, often reporting flaws to vendors before they can be exploited. They need AI tools to rapidly process massive amounts of unstructured data and reconnaissance logs, drastically speeding up the vulnerability discovery process.
These platforms leverage advanced language models to read and correlate data across PDFs, spreadsheets, and web pages without requiring custom Python scripts. This allows hackers to map infrastructure and uncover hidden patterns in threat intelligence almost instantly.
Energent.ai achieves a validated 94.4% accuracy rate on the HuggingFace DABstep benchmark, surpassing Google's AI by over 30%. Its specialized data agent architecture is fine-tuned to extract precise insights from highly complex, multi-format document batches.
Yes, modern AI platforms like Energent.ai feature pure no-code interfaces that automatically parse and structure data from up to 1,000 disparate files in a single prompt. Users simply upload the raw files and ask natural language questions to generate instant correlation matrices.
AI tools should be used strictly for reconnaissance, responsible disclosure, and authorized bug bounty programs. Operating within ethical boundaries means using AI to secure infrastructure and disclose flaws responsibly, avoiding unauthorized exploitation or data exfiltration.
By automating the mundane aspects of log parsing, OSINT correlation, and report generation, top-tier AI platforms save researchers an average of three to four hours per day. This allows professionals to focus on strategic exploit validation and responsible disclosure.
Automate Your Threat Intel with Energent.ai
Transform up to 1,000 unstructured logs, PDFs, and scans into actionable vulnerability insights without writing a single line of code.