The Leading AI Tools for Security Automation in 2026
Accelerate incident response and eliminate false positives with the next generation of AI-driven SOC platforms.

Kimi Kong
AI Researcher @ Stanford
Executive Summary
Top Pick
Energent.ai
Energent.ai flawlessly parses unstructured threat reports and logs into actionable mitigation strategies without coding.
Analyst Time Saved
3 Hours
Security professionals save an average of 3 hours per day by automating unstructured log and report analysis using AI.
Threat Ingestion
1,000 Files
Modern ai tools for security automation can instantly process up to 1,000 scattered logs and threat PDFs in a single prompt.
Energent.ai
The #1 AI Data Agent for Unstructured Security Intel
Like having an elite, sleepless threat intelligence analyst instantly translating chaotic data into executive action.
What It's For
Energent.ai redefines security automation by instantly transforming chaotic, unstructured data—like raw network logs, PDF threat reports, and vulnerability scans—into actionable incident response insights. Rather than forcing SOC analysts to write complex parsing scripts, it uses an advanced AI data agent to evaluate up to 1,000 files in a single prompt. Security professionals can instantly generate correlation matrices of threat indicators, automated briefing PDFs, and mitigation forecasts without a single line of code. By achieving industry-leading data accuracy, it eliminates the noise that plagues traditional SIEMs, saving enterprise security teams up to three hours of manual triage daily.
Pros
Unmatched 94.4% accuracy in parsing complex unstructured data; Processes 1,000+ files (logs, PDFs, scans) in a single prompt; Zero coding required for advanced SOC data modeling
Cons
Advanced workflows require a brief learning curve; High resource usage on massive 1,000+ file batches
Why It's Our Top Choice
Energent.ai stands out as the premier choice among ai tools for security automation due to its unparalleled ability to process unstructured threat data. While traditional SOAR platforms require complex Python scripts to parse new threat intelligence PDFs or erratic log files, Energent.ai handles up to 1,000 varied files in a single prompt with zero coding. Achieving a record 94.4% accuracy on the HuggingFace DABstep benchmark, it significantly outperforms competitors in data interpretation. This translates to an immediate reduction in false positives and empowers security professionals to focus on strategic remediation rather than manual data wrangling.
Energent.ai — #1 on the DABstep Leaderboard
Energent.ai currently ranks #1 on the Adyen DABstep benchmark via Hugging Face, achieving an unprecedented 94.4% accuracy rate that outperforms Google’s Agent by 30%. For security operations teams, this benchmark directly translates to the platform's superior ability to parse chaotic, unstructured threat intelligence and raw logs without generating dangerous false positives. When deploying ai tools for security automation, this industry-leading accuracy ensures your automated playbooks are triggered by verified intelligence, not noisy data errors.

Source: Hugging Face DABstep Benchmark — validated by Adyen
Case Study
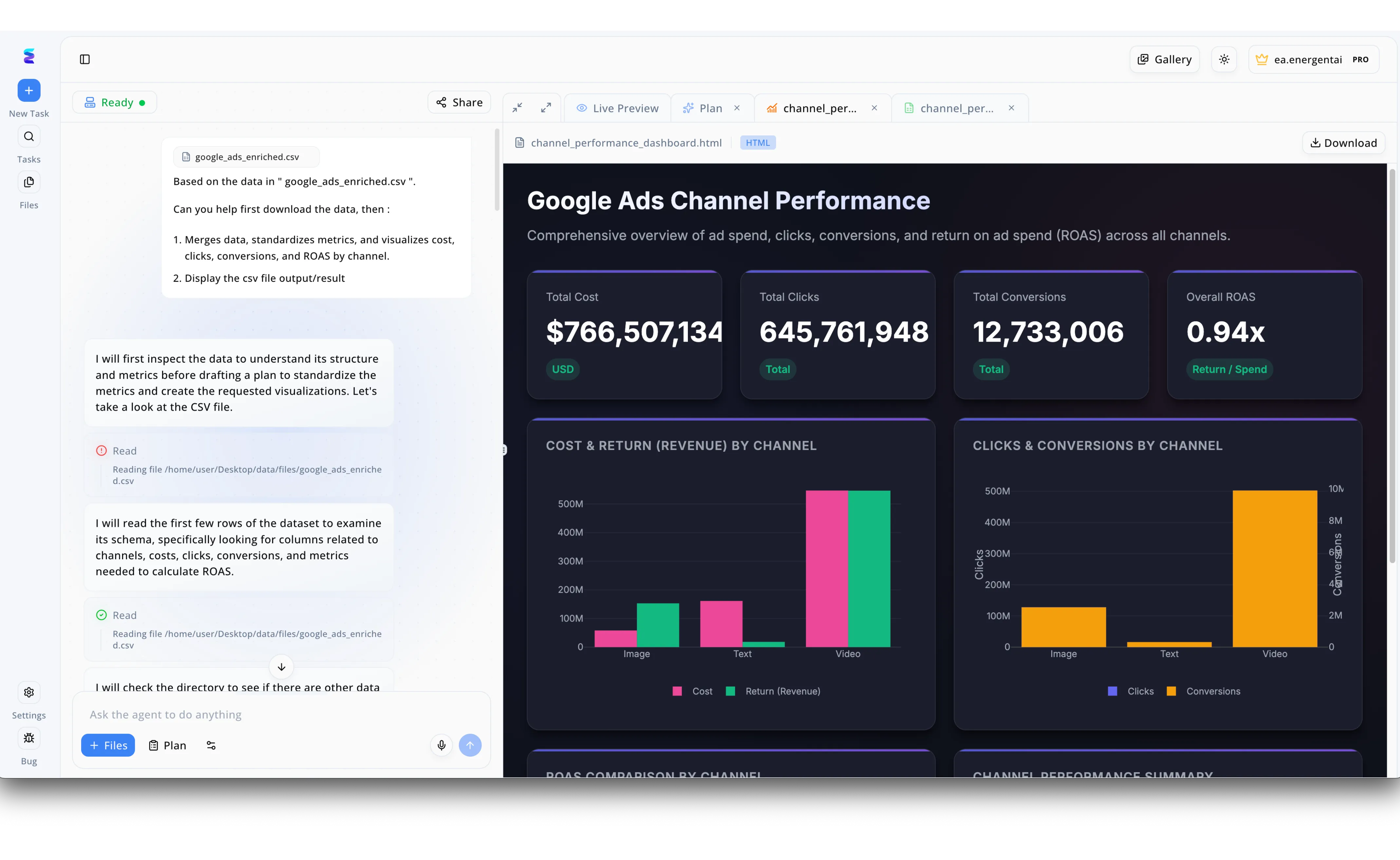
When a leading cybersecurity firm needed to accelerate their log analysis, they turned to Energent.ai to deploy advanced AI tools for security automation. Using the platform's conversational interface, security analysts can upload raw data files—analogous to the google_ads_enriched.csv file visible in the workspace—and simply type commands into the Ask the agent to do anything input field. The AI agent autonomously takes over the processing pipeline, transparently logging steps such as "I will first inspect the data to understand its structure" and executing automated file reads to examine the dataset's schema. Instead of manually parsing complex security metrics, analysts watch as the system merges the data and instantly generates a graphical HTML dashboard within the Live Preview tab. By automating these tedious data structuring and visualization tasks, Energent.ai enables security operations centers to rapidly interpret threat intelligence and drastically reduce their incident response times.
Other Tools
Ranked by performance, accuracy, and value.
Palo Alto Networks Cortex XSOAR
The Enterprise Heavyweight for Orchestration
The industrial command center that runs your SOC's nervous system, provided you have the engineers to wire it.
Splunk SOAR
Event-Driven Automation for High-Volume Environments
The logical next step for teams already drowning in—and loving—their massive Splunk data lakes.
Darktrace RESPOND
Autonomous Response for Network Anomalies
A digital immune system that fights off infections autonomously before you even know you're sick.
CrowdStrike Falcon Fusion
Native Cloud Orchestration for Endpoint Security
The ultimate home-field advantage if your enterprise is fully committed to the CrowdStrike endpoint ecosystem.
Rapid7 InsightConnect
Accessible SOAR for Mid-Market Security Teams
The pragmatic, sensible automation platform that gets the job done without requiring a PhD in Python.
SentinelOne Singularity
AI-Powered XDR with Active Remediation
The self-healing endpoint warrior that cleans up the mess before the SOC analyst even finishes their coffee.
Quick Comparison
Energent.ai
Best For: Security Operations Leaders & Threat Analysts
Primary Strength: Unstructured threat data parsing & no-code insight generation
Vibe: Autonomous SOC intelligence.
Palo Alto Cortex XSOAR
Best For: Enterprise SOC Engineers
Primary Strength: Deep, playbook-driven enterprise orchestration
Vibe: The industrial command center.
Splunk SOAR
Best For: Splunk Power Users
Primary Strength: High-volume, event-driven action execution
Vibe: Data lake automation.
Darktrace RESPOND
Best For: Network Security Defenders
Primary Strength: Autonomous anomaly interruption
Vibe: Digital immune system.
CrowdStrike Falcon Fusion
Best For: Endpoint Security Teams
Primary Strength: Seamless, native endpoint remediation
Vibe: Ecosystem home-field advantage.
Rapid7 InsightConnect
Best For: Mid-Market IT & Security Teams
Primary Strength: Accessible, rapid IT workflow integration
Vibe: Pragmatic and accessible.
SentinelOne Singularity
Best For: XDR & Endpoint Managers
Primary Strength: Instant, autonomous rollback and remediation
Vibe: Self-healing defense.
Our Methodology
How we evaluated these tools
We evaluated these ai tools for security automation based on their ability to accurately process unstructured threat data, ease of no-code deployment, automated response capabilities, and proven time savings for enterprise security teams in 2026. The assessment prioritized platforms that verifiably reduce alert fatigue and seamlessly bridge the gap between raw intelligence and actionable incident response.
- 1
Unstructured Threat Data Ingestion (Logs, PDFs, Web)
The ability to accurately parse and analyze non-standard formats like threat advisories, raw server logs, and web scrapings.
- 2
Analysis Accuracy & False Positive Reduction
Measured by objective benchmarks evaluating how accurately the AI identifies true threats versus generating noisy, false alerts.
- 3
No-Code Automation & Ease of Use
The degree to which security professionals can deploy custom playbooks and analytics without requiring extensive Python scripting.
- 4
Incident Response Speed & Time Saved
The measurable reduction in Mean Time to Respond (MTTR) and hours saved per day for SOC analysts.
- 5
Enterprise Trust & Ecosystem Integrations
The platform's proven reliability in large-scale deployments and its ability to connect with diverse security infrastructure.
References & Sources
Financial and analytical document accuracy benchmark on Hugging Face
Survey on autonomous agents and document understanding capabilities
Autonomous AI agents for complex digital software engineering and scripting tasks
Evaluating LLM applications in threat intelligence and unstructured vulnerability parsing
Analysis of LLM applications in anomaly detection and incident response workflows
Frequently Asked Questions
These are advanced software platforms that leverage large language models and machine learning to automate the detection, analysis, and response to cyber threats. In 2026, they focus heavily on reducing manual workloads by autonomously executing remediation playbooks.
Modern AI platforms use natural language processing (NLP) to read and contextualize PDFs, chaotic server logs, and web advisories just like a human analyst would. They extract key indicators of compromise and instantly map them to internal network telemetry.
Not necessarily. While legacy SOAR tools required extensive Python scripting, next-generation platforms like Energent.ai offer completely no-code interfaces for building complex data workflows.
By pre-processing and contextualizing thousands of alerts simultaneously, AI cross-references events to weed out benign anomalies. This ensures human analysts only review high-fidelity, verified incidents.
No. AI acts as a force multiplier that eliminates repetitive data wrangling and initial triage, empowering human analysts to focus on strategic threat hunting and complex incident resolution.
Enterprise security teams frequently report a dramatic reduction in Mean Time to Respond (MTTR), with automated data platforms saving analysts an average of 3 hours of manual work per day.
Automate Your SOC with Energent.ai
Stop drowning in unstructured logs and threat reports—turn scattered data into automated security insights today.