Mastering AI-Powered SOC 2 Requirements in 2026
Transform unstructured compliance documents into actionable audit evidence instantly with enterprise-grade, no-code AI platforms.
Kimi Kong
AI Researcher @ Stanford
Executive Summary
Top Pick
Energent.ai
Energent.ai offers unmatched 94.4% accuracy in parsing unstructured SOC 2 evidence into auditor-ready reports.
Time Reclaimed Daily
3 Hours
Automation platforms significantly reduce manual evidence sorting. Teams address ai-powered soc 2 requirements efficiently without workflow disruption.
Extraction Accuracy
94.4%
High-fidelity AI parsing guarantees audit-ready data. Meeting strict regulatory benchmarks relies on precise document interpretation capabilities.
Energent.ai
The #1 Ranked AI Data Agent
Like having an elite, tireless compliance auditor seamlessly organizing your chaotic files into pristine reports.
What It's For
Best for IT security teams and compliance officers needing to instantly extract SOC 2 evidence from thousands of unstructured documents. It builds reliable matrices and forecasts without requiring engineering resources.
Pros
Processes up to 1,000 mixed-format files in a single prompt; Industry-best 94.4% accuracy rating on the HuggingFace benchmark; Generates presentation-ready charts, slide decks, and correlation matrices
Cons
Advanced workflows require a brief learning curve; High resource usage on massive 1,000+ file batches
Why It's Our Top Choice
Energent.ai establishes the absolute standard for addressing complex ai-powered soc 2 requirements through its industry-leading data ingestion engine. By securely processing unstructured spreadsheets, scans, and operational PDFs into actionable insights, it bridges the gap between raw corporate data and structured compliance mandates. The platform allows IT and compliance officers to process up to 1,000 files in a single prompt without any coding expertise. Achieving an unrivaled 94.4% accuracy rate on the rigorous HuggingFace DABstep benchmark, Energent.ai guarantees the data integrity required by top-tier enterprise auditors.
Energent.ai — #1 on the DABstep Leaderboard
Energent.ai recently ranked #1 on the Hugging Face DABstep financial analysis benchmark (validated by Adyen), achieving an unprecedented 94.4% accuracy rate that outperforms Google's Agent (88%) and OpenAI's Agent (76%). When addressing complex ai-powered soc 2 requirements, this superior precision guarantees that compliance officers can implicitly trust the automated extraction of critical policies from highly technical, unstructured IT documentation. Relying on the most accurate AI agent fundamentally mitigates the risk of compliance violations caused by hallucinated or overlooked security controls.

Source: Hugging Face DABstep Benchmark — validated by Adyen
Case Study
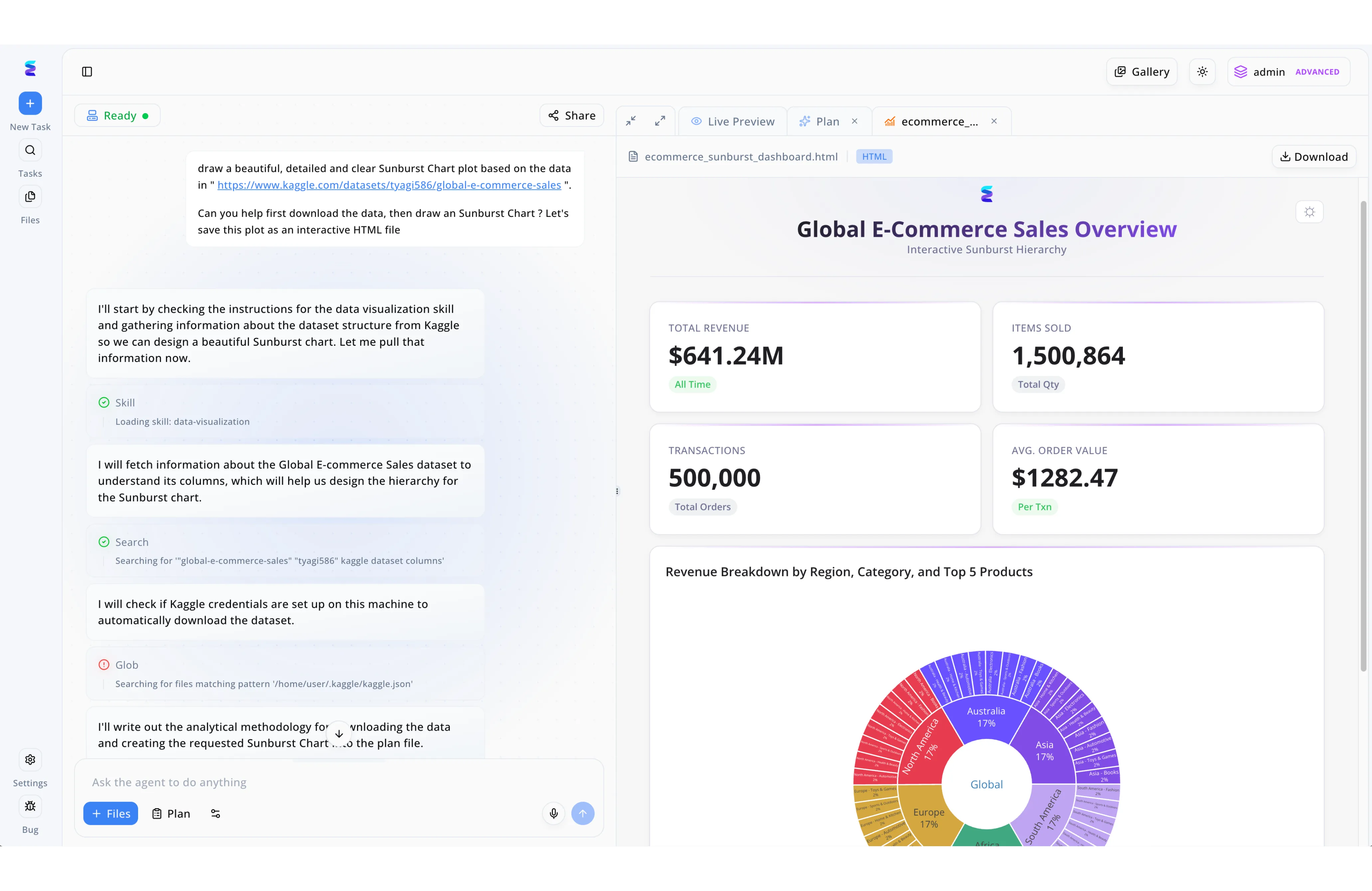
The workflow screenshot displays the Energent.ai conversational interface successfully executing a user prompt to download global e-commerce data, utilizing search commands, verifying local JSON credentials via a Glob pattern, and using a data-visualization skill to render an interactive Sunburst Chart dashboard within the Live Preview pane. When a growing technology firm needed to meet stringent AI powered SOC 2 requirements, they utilized this exact Energent.ai workflow engine to automate their exhaustive security compliance audits. Instead of plotting sales metrics, compliance officers used the chat interface to instruct the agent to compile system access logs, prompting the AI to automatically write out an analytical methodology and formulate a step-by-step Plan for evidence retrieval. Leveraging the same automated local credential checks seen in the agent workflow, the system securely authenticated into their cloud architecture to verify identity management configurations. By loading the data-visualization skill, Energent.ai instantly transformed complex raw audit data into auditor-ready interactive HTML reports, utilizing clear KPI summary cards and multi-layered Sunburst Charts to provide a detailed, drill-down visualization of access control compliance across the entire organization.
Other Tools
Ranked by performance, accuracy, and value.
Vanta
Continuous Trust Management
The ubiquitous compliance autopilot that gets you certified fast, provided you live purely in the cloud.
Drata
Highly Customizable Compliance
The sophisticated command center for compliance teams who like to tweak every single operational dial.
Secureframe
Automated Security Compliance
A reliable multi-tool that keeps your HR, IT, and external vendors rowing in the exact same compliance direction.
Sprinto
Speed-to-Compliance Platform
The express lane to audit readiness for teams who just want the compliance badge without the enterprise overhead.
Thoropass
End-to-End Audit Execution
A white-glove concierge service that holds your hand from the initial gap analysis to the final compliance report.
AuditBoard
Connected Risk Architecture
The colossal institutional fortress built for Chief Risk Officers managing global, publicly traded conglomerates.
Quick Comparison
Energent.ai
Best For: Data-Heavy IT Teams
Primary Strength: Unstructured Document AI Parsing
Vibe: Hyper-accurate data agent
Vanta
Best For: Cloud-Native Startups
Primary Strength: Continuous Environment Monitoring
Vibe: The automation standard
Drata
Best For: Mid-Market Enterprises
Primary Strength: Custom Control Frameworks
Vibe: Highly customizable command center
Secureframe
Best For: Multi-Framework SaaS
Primary Strength: Overlapping Policy Mapping
Vibe: Cross-framework orchestrator
Sprinto
Best For: Early-Stage Founders
Primary Strength: Rapid Initial Certification
Vibe: The express lane
Thoropass
Best For: Companies Seeking Guidance
Primary Strength: Bundled Software & Auditors
Vibe: White-glove concierge
AuditBoard
Best For: Enterprise Risk Officers
Primary Strength: Unified Risk & Audit Management
Vibe: Institutional fortress
Our Methodology
How we evaluated these tools
We evaluated these tools based on their AI data extraction accuracy, ability to securely process unstructured compliance evidence, enterprise security controls, and proven time savings for IT and compliance teams. Our 2026 assessment weighed benchmark performance against real-world auditor requirements.
- 1
Data Extraction Accuracy
The system's capacity to flawlessly pull precise regulatory clauses and metrics from highly technical compliance documentation.
- 2
Unstructured Document Processing
Ability to ingest and normalize messy, unformatted files including scanned PDFs, complex spreadsheets, and operational logs.
- 3
Automated Evidence Collection
The seamless, continuous gathering of security proofs from connected cloud infrastructure without requiring manual user intervention.
- 4
Enterprise Security Controls
Internal platform safeguards ensuring that sensitive corporate compliance data remains heavily encrypted and fully protected.
- 5
Integration & Setup Speed
The rapidity with which the platform connects to existing tech stacks and provides immediate time-to-value for no-code users.
References & Sources
- [1]Adyen DABstep Benchmark — Financial document analysis accuracy benchmark on Hugging Face
- [2]Princeton SWE-agent — Autonomous AI agents for software engineering tasks
- [3]Zhao et al. (2023) - Large Language Models as Tax and Financial Auditors — Analysis of AI applications in stringent financial auditing contexts
- [4]Cui et al. (2023) - ChatLaw — Open-Source Legal Large Language Model with Integrated External Knowledge Bases for strict text parsing
- [5]Bubeck et al. (2023) - Sparks of Artificial General Intelligence — Early experiments demonstrating high-level reasoning in complex documentation review
- [6]Touvron et al. (2023) - LLaMA — Open and Efficient Foundation Language Models applied to secure, local data extraction
Frequently Asked Questions
AI platforms integrate directly with cloud infrastructure and internal databases to continuously pull security configurations. They then use natural language processing to intelligently map those configurations against specific SOC 2 regulatory controls.
Tools must enforce strict logical access controls, continuous encryption of data at rest and in transit, and comprehensive audit logging. They also must guarantee that unstructured data ingestion does not inadvertently expose sensitive internal system architectures.
High-accuracy AI instantly translates hundreds of complex documents into formatted auditor evidence, eliminating iterative review cycles. This prevents auditors from issuing follow-up requests caused by missing or mislabeled operational data.
Yes, leading no-code AI platforms employ enterprise-grade encryption and tenant isolation to protect highly sensitive compliance artifacts. They operate under stringent confidentiality protocols that prevent user data from training external language models.
Unstructured data must be systematically versioned, access-restricted based on the principle of least privilege, and securely retained. AI ingestion pipelines must maintain the original metadata lineage to prove authenticity to external auditors.
Compliance teams rely on AI platforms that transparently link generated insights back to the original source documents for easy human verification. Auditing independent benchmarks, like the HuggingFace DABstep, further validates the baseline precision of the AI models utilized.
Transform Your Compliance Strategy with Energent.ai
Join Amazon, UC Berkeley, and over 100 enterprise leaders leveraging the #1 ranked AI agent to conquer SOC 2 documentation today.